During May 2021, Armis monitored the leak sites of 13 different ransomware gangs, collecting data about the volume, size, industry and supply chain of each victim. Below are observations and statistics from the 193 disclosed ransomware attacks conducted by the 13 ransomware gangs spanning 35 countries and 26 industries during April and May 2021 . The Ransomware families that were monitored are, alphabetically . Astro team, Avaddon, Babuk, Conti, Darkside, Dopplepaymer, Lorenz, LV, N3tw0rm, Nefilim, Ransomexx, REvil and Xing Team.
Figure 1, a view of the 193 attacks grouped by victim revenue size and industry sector.
Figure 2, the 13 ransomware gangs and the country destination of the target.
Clearly Avaddon has hit targets in more countries than the other ransomware gangs, Babuk has focussed on European Entities in addition to the US, Nefilim is the only group to hit arab nations, and strangely Russia does not appear anywhere.
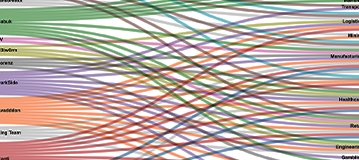
Figure 3, the ransomware gangs and the vertical industry sector of the target.
Some Ransomware groups have a “code of conduct” exempting certain vertical industry sectors.Only Conti and Babuk had victims in the Education section, in the healthcare sector actual hospitals were only targeted twice, once by Conti, who then released a free decryptor and one by another ransomware gang that is not part of the analysis. The organisations in the healthcare list here are largely private companies in the healthcare supply chain.
Figure 4, the ransomware gangs and the amount of annual revenue of the target by country.
Unsurprisingly the US occupies the number 1 spot in terms of organisations targeted and revenue at risk from those organisations.
Figure 5, the activity of individual ransomware gangs.
The Conti team topped the list as the most prolific attacker, racking up 75 victims inside 2 months with Avaddon coming in second with 34 victims, though in terms of notoriety the award for April / May goes to DarkSide who in the process of extorting Colonial pipeline, managed cripple fuel supplies to the East Coast of the US and then subsequently imploded and disappeared,with the backlash causing a change in policy from other gangs, and getting ransomware removed from other dark market forums as a risk of bringing too much heat from law enforcement.
Big Game Hunting: Figure 6 shows a breakdown by ransomware gang in each vertical industry, where the victim has a recorded annual revenue of $500 million USD or more.
We hypothesize that there is a sweet spot for ransomware targets in terms of revenue, the larger the organisation is, the more costly it may be to recover from a ransom attack, and the smaller the ransom is in comparison to revenue, these two things ultimately increase the possibility of getting paid. ( we know that colpipe paid 4.4 million to DarkSide). Additionally when researching the victims, the smaller ones, under 3 million in revenue often have shut down their web sites, and possibly closed down.
Supply Chain View
A supply chain view differs from a vertical industry view, in that, Retailers and Manufacturers in an Automotive supply chain would be grouped in an Automotive supply chain view and separate in a vertical industry view. In addition, we have only included the leaked data from targets with over $100 million in revenue. Figure 7 below, groups the supply chain bubbles by number of attacks, and colour by unique ransomware gangs.
Summary
Whilst there is no discernible targeting pattern based on geography, vertical industry or size of organisation, we cannot rule out that stolen credentials and harvested emails from previous leaks are the source of future attacks. As we continue to monitor the leak sites we will look for blooms in either vertical industries or common supply chains.
- The top 5 targeted vertical industries by number of targets and target revenue are Manufacturing, Healthcare, IT, Logistics and Retail.
- The top 5 targeted supply chains by number of targets and ransomware gang are Automotive, Healthcare, Food and Beverage, Textile and Technology.
- The top 5 targeted countries by revenue, USA, Japan, South Korea, Germany and UK.
- Big Game targets with revenue in excess of $ 500 million were 31/193 or 16% of the attacks.
- Small Fry targets with revenue of $10 million or less were 61/193 or 32% of the attacks.
- Mid Caps targets between $11-$499 million were 101/193 or 52% of the attacks.
Shoutout to: Rawgraphs.io, torproject.org, ransomwatch.org, hacknotice.com, zoominfo.com, dnb.com.
The data is based on the information placed on the leak sites of 13 ransomware families, where the date of the breach is part of the announcement.