By Ben Seri, Yuval Sarel and Gal Levy
In the recent Patch Tuesday, June 8, 2021, Microsoft patched CVE-2021-31958 – a vulnerability affecting the MSRPC service discovered by Armis’ researchers. This vulnerability enables an attacker to relay NTLM authentication and open a privileged session with the Event Viewer service, remotely. With this session an attacker can leak local event logs from a target device, leak file information metadata, flood the file system causing resource exhaustion and override critical files causing permanent DoS.
Similar vulnerabilities in the attack surface of NTLM authentication were previously discovered (here here) and successfully exploited and this recent vulnerability can be triggered using the same attack flow, but by targeting a different service (the Event Service). To understand how this vulnerability could be exploited, some background on NTLM Relay attacks is needed. Since this topic was extensively covered in recent related works, this blog will only provide a brief overview of this attack vector.
NTLM Relay
Authentication between two Windows devices is performed, by default, using NTLM authentication. Using a challenge provided by the server, a client uses its credentials to authenticate itself with the server and access privileged services. NTLM Relay attacks are essentially a Man-in-the-middle (MiTM) attack on the NTLM authentication process, allowing an attacker to open a privileged session with the server without actually acquiring the required credentials.
To prevent these attacks, most Windows services enforce a more strict authentication standard. This is done by authenticating each packet in the session, meaning the relay would need to happen for each packet, preventing an attacker the ability to control how the credentials are used. Specifically for MSRPC, there are 7 levels of authentication each process can enforce:

From Microsoft’s docs
Event Viewer Service RPC Relay
To quickly understand the vulnerability, let’s examine the patch Microsoft implemented via KB5003637:
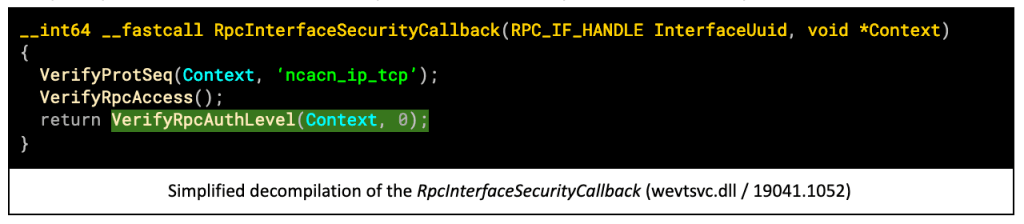
The function RpcInterfaceSecurityCallback is responsible (as mentioned in its name) for verifying some security aspects of the RPC authentication level, for the Event Service. The function call highlighted in green was added in the latest patch and before its addition the return value of the function was always 0, indicating success. The function VerifyRpcAuthLevel verifies, among other things, that the authentication level of the RPC session is 5 or higher (meaning at least RPC_C_AUTHN_LEVEL_PKT_INTEGRITY). Prior to the patch an attacker could fully control the authentication level, including RPC_C_AUTHN_LEVEL_CONNECT.
This level of authentication enables an attacker to relay NTLM credentials and open an authenticated MSRPC connection to the Event Viewer service. To understand the implications of an attacker opening such a connection, we need to review some of the capabilities exported by this service.
Event Viewer Primitives
There is a lot of potential usage for this service to an attacker. Beside the trivial but important usage of remotely accessing the events logged by this service (allowing an attacker to disclose sensitive information from the target), we’ve found three additional primitives that may elevate the severity of this attack vector.
Remote File Override
After connecting to the Event Viewer Service, an attacker could use EvtRpcExportLog command to export an event log file to a path of his choosing. The available paths are in correlation with the privileges of the credentials relayed to the target. With an administrator’s privileges, an attacker could override critical files in the system (e.g. in C:/windows/system32), which could disrupt the machine considerably — even preventing it from booting after a reset (permanently, until fixed). With lower privileges an attacker can override applications’ data files and user data, which can obviously be quite disruptive to end-users.
Remote File System Resource Exhaustion
In a similar fashion, an attacker could use the same command to export an event log file (which should be several MBs in size) to a path that doesn’t override an existing file. Calling this API repeatedly, with different file paths each time, can fill up the disk space of the target within a short period of time. This could have DoS implications to the target, either by slowing down its machine or by preventing certain applications which require free disk space from operating as intended.
Remote File System Mapping
Another primitive available to an attacker, is using the hEvetRpcOpenLogHandle command to open a log file. The service does not verify that this file is in fact a log file, and thus it could be any file on the file system. Combining this command with the hEvtRpcGetLogFileInfo with certain arguments, an attacker can retrieve metadata attributes on any file in the target’s file system given a known path. This information leak primitive can enable an attacker (for example) to determine the target’s exact build version (by drivers’ sizes), or to find out the brand and version of installed security agents (EDRAV) — also, by leaking certain file attributes.
Putting it All Together
To summarize, let’s review an attack scenario with real life implications. This scenario takes place in an OT environment. In this type of environment, it is common for IT users to use remote desktop connections, to manage engineering workstations. Establishing a Man-in-the-middle position on such a connection can allow an attacker to intercept an NTLM authentication process, and abuse it for accessing the Event Viewer Service.

- The attacker establishes a MiTM position between a technician and an Engineering Workstation, by ARP spoofing the IP of the Engineering Workstation, and ambushing a technician’s RDP connection.
- A Technician initiates an RDP connection to the Engineering workstation and an NTLM authentication request is intercepted by the attacker.
- The attacker passes the request to the Engineering workstation which generates an NTLM challenge that is solved by the technician’s machine, and passed back to the Engineering workstation.
- Having successfully relayed the NTLM authentication, the attacker opens an Event Viewer session with the engineering workstation, and overrides critical files — leading to denial-of-service.
This attack could prove fatal to the flow of an OT’s environments’ continuous work. Engineering workstations in these environments contain critical databases, which are not usually backed up automatically.
How Armis Can Help
Thankfully, the use of outdated authentication levels via RPC connections is gradually becoming more and more scarce due to security disclosures such as this. However, in legacy systems, in OT and healthcare environments and in many additional applications, unpatched Windows devices are a common occurrence. The Armis platform monitors the use of RPC connections, the level of authentication in use, and can alert users when an insufficient authentication level is being used. In addition, detecting ARP spoofing and other MiTM attacks that can facilitate NTLM relay attacks can also be detected using the Armis platform.







